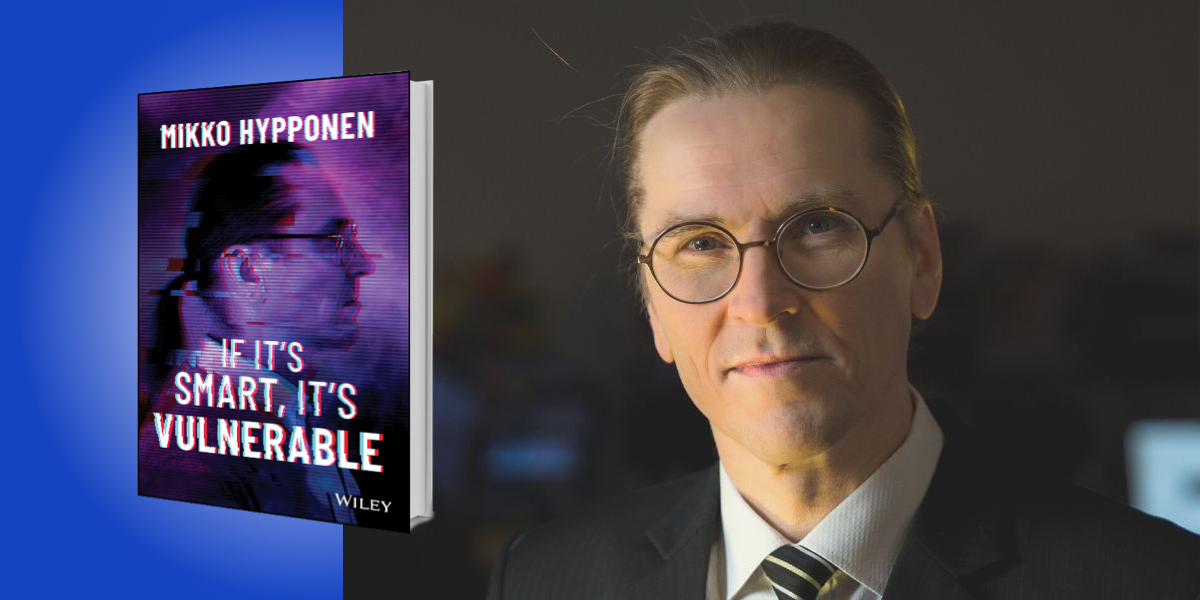
Mikko Hypponen is a global cybersecurity expert with over 30 years’ experience working as a researcher and investigator. He has written about his research for the New York Times, Wired, and Scientific American, and he appears frequently on international TV.
Below, Mikko shares 5 key insights from his new book, If It’s Smart, It’s Vulnerable. Listen to the audio version—read by Mikko himself—in the Next Big Idea App.
1. Every hack, malware outbreak, or data leak can be traced back to either a technical vulnerability or human error.
Technical problems and vulnerabilities might be really hard, slow, and expensive to fix, but at least we can fix them. We find the vulnerability in the code, the mistake that the programmer made, we fix it, and then we make sure everything is updated.
But there is no software update for a human brain. The only way we can fix people who make mistakes is by education—though education almost always fails. This is the only way we can prevent people from using the same password everywhere, installing every application they see, falling for every phishing scam, and clicking open every attachment and every link.
It’s also important to understand who we are fighting. When I started analyzing viruses in the early 1990s, they were spreading on floppy disks. The authors of these old viruses were teenage boys—they were writing them for fun. But today, the hacks, malware, and online attacks are coming from organized online crime gangs. I’ve started calling these gangs “cybercrime unicorns,” as a reference to “unicorn” companies, because some of the largest online crime gangs are unicorns for all practical purposes. They hold massive wealth. They are able to hire professionals. They run physical offices.
“Today, wars expand from the real world to the online world.”
But organized online crime gangs are not the only source of attacks. There are also “hacktivists.” These are hacker activists, people who break the law not to make money or benefit themselves directly, but for a higher cause—for a political reason or to make a point, to send a message maybe. The Anonymous Movement is a good example.
We also know that terrorists and extremists use the internet, and potentially not just for communication, recruitment, and radicalization. They could also use it for executing actual terrorist attacks. Now, we haven’t seen that yet, which is almost surprising—but unfortunately, sooner or later, we will.
And then we have nation-states themselves, using cyber offensive action. Governments use malware and hacking for espionage and spying, and they also use it to wage war. Today, wars expand from the real world to the online world.
2. Privacy is dead, and we killed it.
When we were living offline, it was easy to have privacy. Today, it’s impossible. We carry around these tracking devices 24 hours a day—we even sleep next to our mobile phones. Through these tracking devices and our online activity, our lives can be tracked from cradle to the grave. Where are we? Where are we traveling to? Who are we traveling with? Who are we communicating with? What are we communicating about? What do we like? What do we hate? All of this information can be, and actually is being, controlled and collected.
Google, Facebook, LinkedIn, Twitter—all of these companies use this information to make a lot of money. The biggest companies on the planet used to be oil companies, but today, the biggest companies on the planet are data companies. And just like we used to worry about oil leaks, today we worry about data leaks.
3. If it’s smart, it’s vulnerable.
This is known as the Hypponen Law. I said this a couple of years ago at some conference, when I was talking about “internet of things” devices like smart TVs or smart cars. You see, when we add functionality and connectivity into everyday devices, they become hackable.
“When we add connectivity and functionality into everyday devices, they become hackable—that’s the Hypponen Law.”
Take my watch, for example. I’m wearing an old-school mechanical watch on my wrist. How do you hack a mechanical watch? Well, you don’t. There’s nothing to hack—it’s not online. There’s no processor. There’s nothing you could do.
But then we look at modern smart watches, like the Apple Watch. Are they hackable? Of course. It might be hard, but it’s doable because they are online and they run code. When we add connectivity and functionality into everyday devices, they become hackable—that’s the Hypponen Law.
4. War has changed—cyberweapons have become a real thing.
Cyberweapons make a lot of sense from the point of view of militaries, because they are effective, affordable, and deniable. That’s a pretty good combination of features: a weapon that gets the job done, a weapon that is cheaper than alternatives, and best of all, a weapon that you can claim is not your weapon at all. This is why we’ve seen governments use cyberweapons in cyber-sabotages—like in the case of Stuxnet—as well as in cyber-war, like the Russian government using NotPetya against Ukraine.
5. Our devices have never been more secure than they are today.
I know it doesn’t seem that way, but that’s because of what I call “security Tetris.” We all know the rules of the game of Tetris; you’re trying to make a whole line, and when you succeed, the line disappears. In other words, your successes disappear, while your failures pile up. That’s what happens in Tetris, and that’s what’s happening in cybersecurity.
“The best example of the big advancements in cybersecurity are our mobile devices.”
When a company gets hacked, that is big news. But when a company’s IT department works through the night to patch their servers before being hacked, nothing happens. I can guarantee you that tomorrow, the biggest newspaper in your town won’t carry a headline saying that the largest company in our country was not hacked. So when we succeed, it’s unlikely to be noticed by anyone, and rarely is anyone thanked for stopping a disaster that didn’t happen. But the fact is, we’ve never been more secure than we are today.
The best example of the big advancements in cybersecurity are our mobile devices. Our mobile devices are, in many ways, architecturally closer to our game consoles than our computers. You never hear about malware outbreaks or hacks on PlayStations or Xboxes, do you? Why not? Because they’re closed environments—you can only download the games from Sony or Microsoft. Well, that’s exactly the model you have on your iPhone or iPad. It’s a closed environment, which means it’s really restrictive, but also really secure.
So, the situation is getting better. And today, everything runs on computers. So we are not just securing computers—we’re securing the whole society.
To listen to the audio version read by author Mikko Hypponen, download the Next Big Idea App today: