Amy Zegart is a professor, by courtesy, of Political Science at Stanford University and a senior fellow at the Hoover Institution. She is also a contributing editor to The Atlantic, and has been studying U.S. spy agencies for more than two decades.
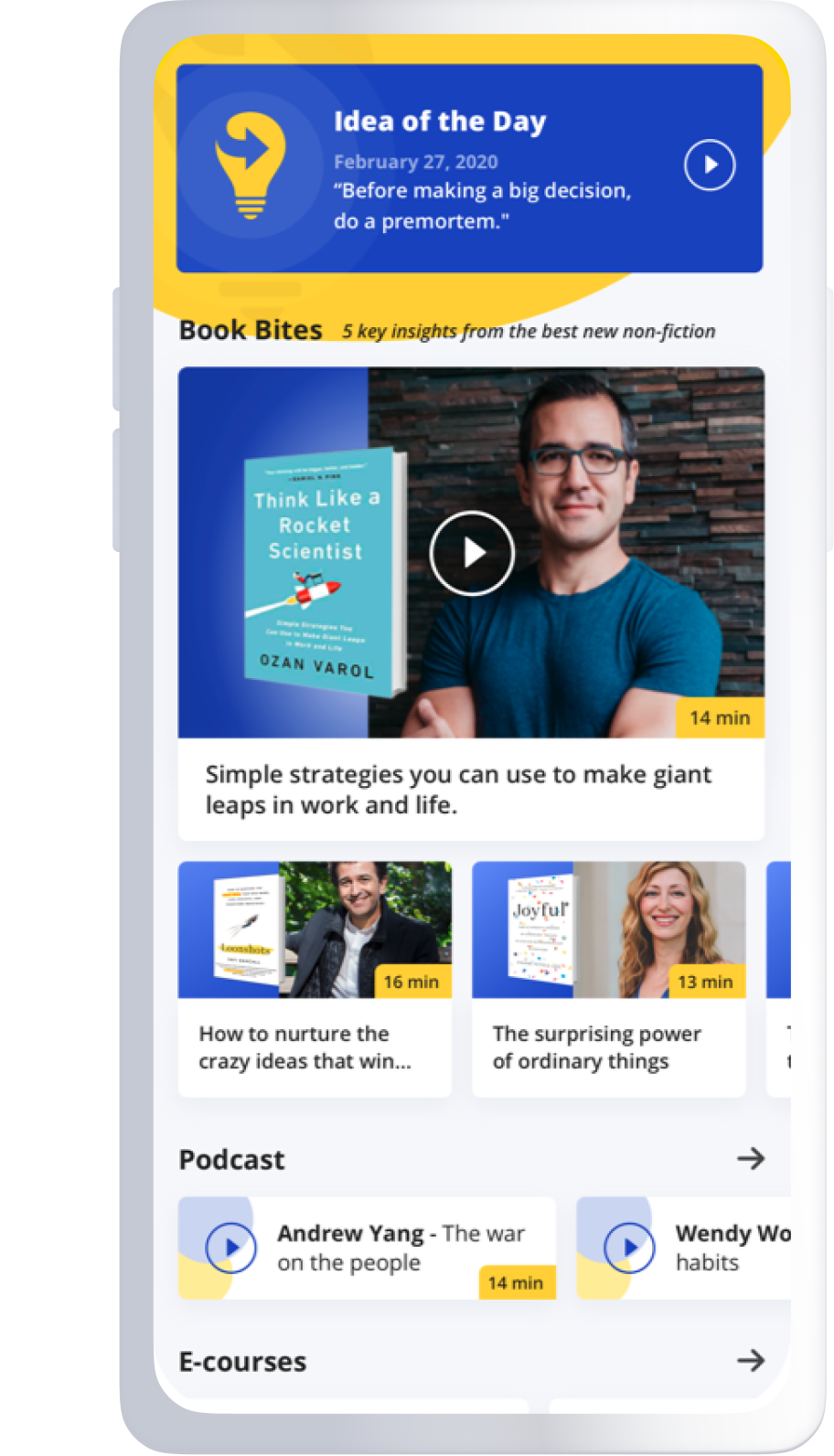
Below, Amy shares 5 key insights from Spies, Lies, and Algorithms: The History and Future of American Intelligence. Listen to the audio version—read by Amy herself—in the Next Big Idea App.
1. Jack Bauer is a bad teacher.
Spy-themed entertainment is big business. Who doesn’t enjoy worlds where Congress works well and the good guys always win? Of course, we all know real spying is different. As one intelligence official told me, “None of us are that good-looking, and we don’t solve anything in just 42 minutes.”
But here’s the thing: when I started polling my own college students, I discovered that spy-themed entertainment was adult education. Characters like Jack Bauer, the star of the hit TV show 24, who saves the U.S. from terrorists by doing “whatever it takes,” are influencing public opinion and real intel policy.
I was so surprised by my student polls that I fielded two national surveys. Americans who said they consumed lots of spy-themed entertainment were far more likely to support controversial activities, like warrantless surveillance of American phone records and waterboarding suspected terrorists. Whether you think these activities are morally right or wrong, effective or ineffective, the fact that fiction influences public attitudes about them is unsettling.
Fictional spies influence policymakers, too. In the fall of 2002, Lieutenant Colonel Diane Beaver, at Guantanamo Bay, ran brainstorming sessions about interrogation techniques. She later admitted that Jack Bauer “gave people lots of ideas.” Beaver later approved the use of dogs, sexual humiliation, and waterboarding.
“Characters like Jack Bauer, the star of the hit TV show 24, who saves the U.S. from terrorists by doing ‘whatever it takes’ are influencing public opinion and real intel policy.”
In 2009, the Senate Intelligence Committee held a confirmation hearing for Leon Panetta to become Director of the Central Intelligence Agency. Senators asked what interrogation techniques Panetta might use if confronted with someone in custody who is thought to have info about an imminent attack. Panetta took this hypothetical seriously, even though experts have long argued that “ticking time bomb” scenarios are unrealistic and only happen in the movies.
Spy-themed entertainment has even penetrated the CIA. You might remember Zero Dark Thirty, the Academy Award-nominated film about the hunt for Osama bin Laden. The movie generated so much confusion and controversy about what was real that the CIA’s Acting Director had to issue a memo to the workforce. He wrote, “The film takes significant artistic license, while portraying itself as historically accurate.” When the head of the CIA has to debunk a movie about the CIA to the CIA, you know entertainment is not just entertainment.
2. Spying isn’t just for governments anymore.
Thanks to the internet, artificial intelligence, the commercial satellite revolution, and other emerging technologies, spying isn’t just for governments anymore.
In the old days, government dominated the collection and analysis of information with billion-dollar satellites and spy networks. Now, data is everywhere and accessible to just about anyone. More than half of the world is online. More people have cell phones than running water. Anyone with an internet connection can get Google Earth satellite images, identify people using facial recognition software, and track events on Twitter. This kind of publicly available information is called open-source intelligence. It’s a gold mine that is transforming who can track global dangers, and how.
When Russia invaded Ukraine in 2014, the best intelligence came from selfies: time-stamped photos taken by Russian soldiers and posted on social media with U.K. highway signs in the background. Social media has become so important that the consoles at America’s underground nuke command center display Twitter feeds alongside classified intelligence feeds.
“Anyone with an internet connection can get Google Earth satellite images, identify people using facial recognition software, and track events on Twitter.”
Consider this: there is a large and growing ecosystem of nuclear threat detectives. This group looks like it came straight out of the Star Wars bar scene. Some are experts, but most are amateurs. There are hobbyists and activists, volunteers and profiteers, coin dealers and physicists, and everyone in between. None of them have security clearances or work inside a government spy agency, but some of the work they do is incredible. They identified key elements of nuclear programs in Iran and North Korea. Then, more recently, they discovered hundreds of new Chinese nuclear missile silos.
This open-source ecosystem brings risks, too. Errors can go viral. Nobody gets fired for making a mistake. There’s no mandatory quality control or training. All this transparency can make crises harder to manage. When info is public, pressure builds for each side to do something. Backing down becomes harder, and conflict becomes more likely.
3. Cyberspace is the Mad Hatter’s Tea Party.
In the story Alice’s Adventures in Wonderland, the Mad Hatter’s Tea Party turns everything on its head. It’s a world without rules, and it’s riddled by contradictions—which is exactly what cyberspace is.
Think for a minute about the physical world we’re used to. The government is responsible for protecting citizens—hence the police and military. The more powerful a country is, the more it can advance its interests and defend its people. And war is big and obvious, making it easy to tell when the fighting starts.
None of that is true in cyberspace. In cyberspace, the government doesn’t protect your computer systems—even critical industries are pretty much on their own. Power brings vulnerability instead of security, because the most powerful countries (like the U.S.) rely on computer networks for everything: economy, government, society, military. Anything running on code and connected to the internet is a potential cyberattack vector—including items as unexpected as your refrigerator and home appliances.
Then in the case of cyberspace war, it looks small because it’s hidden. Cyberwar is the accumulation of daily breaches that create massive consequences—like intellectual property theft. But it’s hard to know when a weapon is a weapon. Technically speaking, 90 percent of any cyber intrusion looks the same, whether the perpetrator is defending their own networks, attacking something, or gathering intel. When attacks can look like intelligence operations and intelligence operations can look like attacks, the risk of miscalculation is high, and intelligence about an adversary’s intentions matters more.
“Anything running on code and connected to the internet is a potential cyberattack vector—including items as unexpected as your refrigerator and home appliances.”
As if this weren’t hard enough, the cyber battleground is constantly shifting. Every time someone downloads a patch or uses a new app, they change what can be attacked, and how. Waging offensive cyber operations requires intelligence—lots of it, all the time. Cyber is the ultimate cloak-and-dagger battleground.
4. We’re all intelligence customers now.
Intelligence reports used to be produced by people with security clearances for people with security clearances. Even inside this secret government world, information was tightly restricted. In 2011, for example, as intelligence officials closed in on Osama bin Laden’s whereabouts, White House planning meetings were listed in the calendar as “Mickey Mouse” meetings to preserve operational security. Not even the FBI Director or Secretary of Homeland Security knew about them.
Today, more people outside of the government need intelligence to advance national interests and protect the country. Voters need intelligence about foreign interference in American elections. Private-sector leaders own and operate most of America’s critical infrastructure—power, water, transportation, financial services—and they need intelligence about cyber adversaries to prevent disaster. Investors and startup CEOs need to understand how China is buying and spying its way to technological advantage. Tech company leaders at the likes of Facebook, Apple, Amazon, Google, and Microsoft are often on the front lines of information warfare. They have information the government needs, and the government has information they need.
Who’s a decision-maker needing intelligence? Today, increasingly, it’s people who sit in board rooms and in living rooms—not just the White House Situation Room. This is radical new world, and interacting with outsiders is not a natural act for intelligence officers. Once I had a group of CIA officials conduct a simulation for my class, and the public affairs person wouldn’t tell me his last name. This wasn’t some secret mission to a dangerous outpost; it was a pubic engagement trip to an American university. Still, the public affairs person wasn’t comfortable being public.
“Today, more people outside of the government need intelligence to advance national interests and protect the country.”
It’s also a revolutionary shift for American companies, many of which resist the idea that they have any responsibility for national security. But economics and national security are tightly intertwined. Securing advantage means intelligence agencies have to find new ways to work with the private sector and engage the outside world, not stand apart from it.
5. Gray cells need red cells.
Intelligence is in the business of anticipating the future. A big reason this is a tough job is the human brain—our own gray cells. All of us misperceive the world, even when we are trying hard not to, thanks to cognitive biases. These are mental shortcuts we use to make sense of information. We use them without realizing it, like voting party-line tickets rather than carefully researching each candidate for every local office. Cognitive biases can be useful, but they can also lead us astray.
In an experiment, Amos Tversky and Daniel Kahneman gave this description about a woman named Linda: 31 years old, single, outspoken, and very bright. She majored in philosophy. As a student, she was deeply concerned about discrimination and social justice, and also participated in anti-nuclear demonstrations. Tversky and Kahneman then asked which was more probable: Linda is a bank teller, or Linda is a bank teller and is active in the feminist movement.
85-90 percent of people in their study chose #2, that Linda is a bank teller and is active in the feminist movement—but that’s wrong. All feminist bank tellers are also bank tellers, so #1 always has a higher probability of being true. The math doesn’t lie, but the brain often does.
Intelligence failures often stem from cognitive biases. In 1950, General Douglas MacArthur was taken by surprise when Chinese forces entered the Korean War. MacArthur had been so convinced China wouldn’t attack that he discounted the intelligence pouring in that suggested otherwise.
Red cells are one promising way to combat this gray cell problem—essentially the idea of “let me play devil’s advocate.” Red cells take that further; they are teams of people who are designated skeptics with a mandate to push the contrarian view, and challenge assumptions and evidence. After 9/11, CIA Director George Tenet created a CIA Red Cell. He hand-picked its members and gave them wide latitude. As one of them said, “Tenet charged us to piss off senior analysts. If we weren’t doing that, we weren’t doing our jobs.”
Red cells can go a long way toward improving intelligence analysis. As the old saying goes, two heads really are better than one.
To listen to the audio version read by author Amy Zegart, download the Next Big Idea App today: